Crypto-related losses reached $3.4 billion in 2025, but the most striking takeaway from the data is how those funds were stolen.
According to the data chart from Chainalysis, the majority of recent attacks did not rely on sophisticated smart-contract exploits. Instead, they targeted human behavior, personal wallets, phishing links, social engineering, and unsafe approvals.
What the Chart Shows
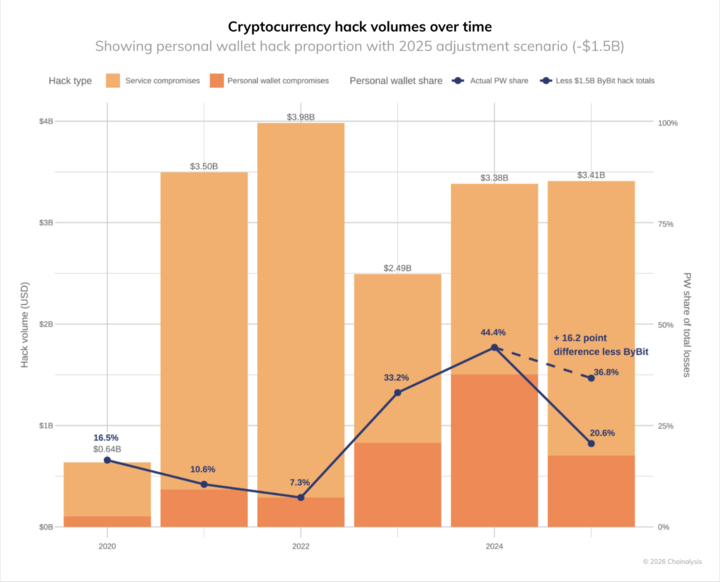
The chart breaks down crypto hack volumes over time, separating service compromises from personal wallet compromises, while also tracking the share of total losses coming from personal wallets.
A few trends stand out clearly:
- Total losses remain elevated: Hack volumes have stayed above $3 billion in recent years, with 2025 ending around $3.41B even after adjustments.
- Personal wallet attacks surged: In 2024, personal wallets accounted for roughly 44.4% of total losses, marking a sharp shift away from centralized service breaches.
- 2025 moderation, but still dangerous: The personal wallet share drops to about 20.6% in 2025, yet this still represents hundreds of millions of dollars lost due to user-level mistakes.
- Human vectors dominate: Even when overall losses fluctuate year to year, the chart shows that attackers increasingly favor methods that exploit user trust rather than protocol vulnerabilities.
Why This Matters
The data reinforces a crucial point: security risks have moved up the stack. As core blockchain infrastructure and major protocols harden their code, attackers are adapting by targeting users directly, through fake websites, malicious links, impersonation scams, and deceptive wallet approval requests.
This explains why even during periods without major protocol failures, losses remain high. The weakest link is no longer the smart contract, it’s the decision made at the moment a wallet signs a transaction.
The Takeaway for Users
The message behind the numbers is simple but urgent:
- Double-check links before clicking.
- Verify messages and impersonated accounts.
- Review wallet approvals carefully, especially blind signature requests.
As the chart makes clear, improving code security alone isn’t enough. In 2025, staying safe in crypto increasingly depends on user awareness, not just developer audits.







